Without security, Team Password Manager would be rather pointless, that's why we've taken extra steps to ensure that our security features are the tightest on the market.
Every time we develop a new feature, it is gauged against its security implications.
Security is our number one priority.
Trusted encryption technology
One of the ways Team Password Manager protects against hacking is by encrypting saved password data in AES-256. AES stands for Advanced Encryption Standard. AES is so trusted, that it has been adopted by the U.S. Government and is used world wide.
Each users' passwords are hashed using Bcrypt, providing further security to the application. Bcrypt is a cross-platform encryption utility that hashes passwords so that they are protected against rainbow tables and brute-force attacks.
By acting together, these two encryption processes form a strong wall of defense to protect against any would-be hackers that would like to get their hands on your password information.
Obfuscated PHP and web application vulnerabilities prevention
If hackers do try to use decryption software to break into the system, it will be nearly impossible due to the fact we use obfuscated PHP code, which prevents crackers from seeing how to decrypt data.
As far as the typical vulnerabilities found in web applications, such as Cross-site scripting (XSS), SQL injection or Cross-site request forgery (CSRF), our programming team has taken special care to fortify the defenses in this area. Some tables even use hash codes to prevent tampering.
Two-factor authentication
In addition to sophisticated encryption protection, Team Password Manager uses two-factor authentication with Google Authenticator, which provides a six digit number users must provide in addition to their username and password in order to login into services.

IP Address Blocking
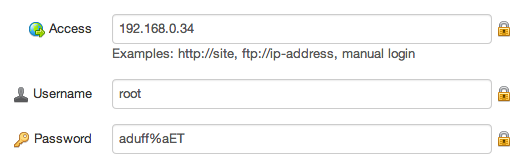
Team Password Manager can be configured to reject access from specific IP addresses, making brute-force attacks difficult or impossible.
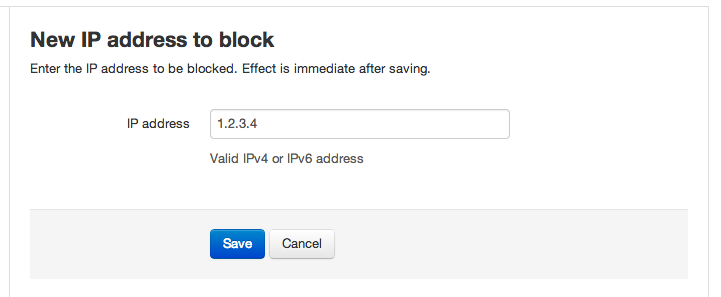
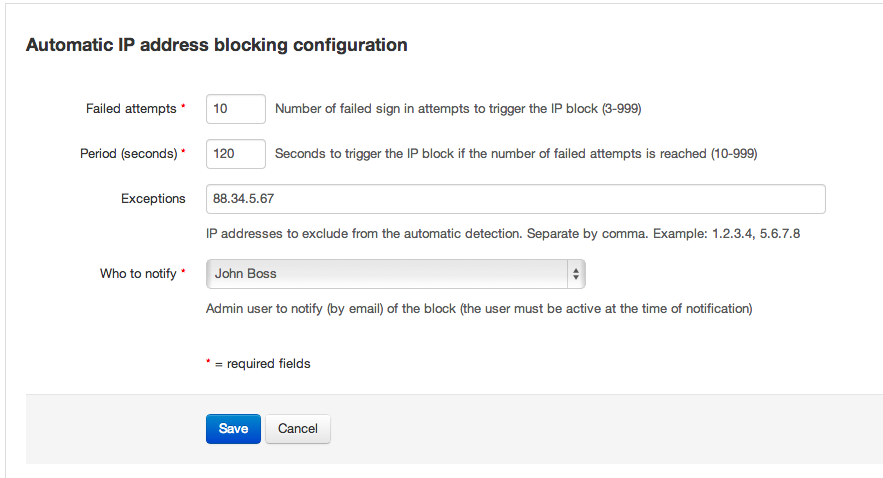
IP address blocking can be configured in two ways: manual and automatic.
In manual IP blocking you just enter the IP addresses you wish to block:
With automatic IP blocking you set an interval (in seconds) and a number of login attempts. If the number of login attempts in this interval is greater than the one set, the offending IP address will be added to the list of blocked IP addresses. You can optionally enter some IP addresses to exclude (that would be your office IP address) and the admin user that will be notified by e-mail when an IP is automatically blocked:
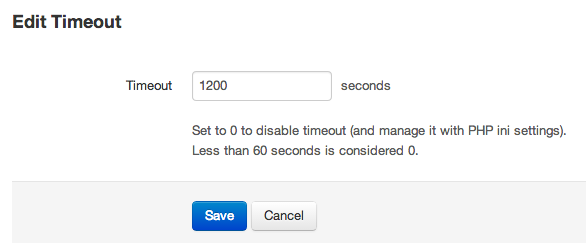
Configurable timeout and auto-logout
You can configure how long you want inactive sessions to last. In addition, the software will auto-logout from a session if the timeout has expired.
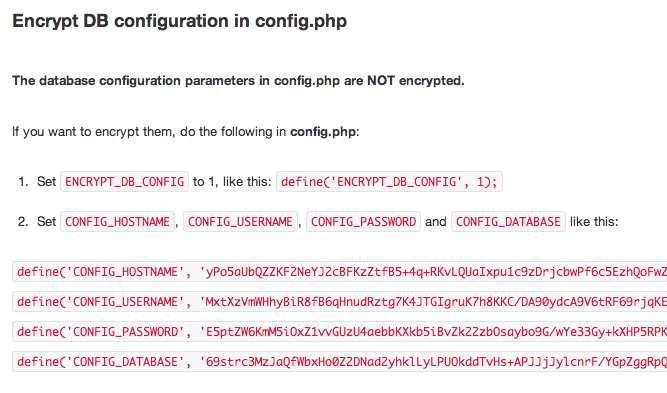
Encrypt database configuration
The database parameters required for Team Password Manager to access the database can be stored as encrypted strings in the main configuration file, thus preventing unauthorised users to read them.