This tutorial explains how to install Team Password Manager on a Linux Ubuntu 24.04 (LTS) system with the following components: Apache 2.4, MySQL 8, PHP 8.4, Sourceguardian Loader and a commercial TLS/SSL certificate for https.
Similar versions of this tutorial with lower versions of the components can be found here: Install on Ubuntu 18.04, Install on Ubuntu 20.04 and Install on Ubuntu 22.04.
A similar version of this tutorial with NGINX instead of Apache can be found here: Install on Ubuntu with NGINX.
To be able to follow this tutorial you'll need: a running Ubuntu 24.04 LTS system (preferably with nothing else installed), which can be accessed from anywhere on the Internet, root access to this system and a non-root user which we'll use to do everything with sudo for security. You'll also need some basic Linux knowledge.
- Basic settings
- Apache installation
- MySQL installation
- PHP installation
- Configuring the web server using Virtual hosts
- HTTPS and installing a commercial SSL Certificate
- SourceGuardian Loader installation
- Team Password Manager database and user
- Team Password Manager files
- Team Password Manager configuration file
- Team Password Manager installation script
Basic settings
We'll be creating a Team Password Manager installation that will be accessed using this URL: https://tpm.mycompany.com. We'll be referring to this URL throughout this document, so adjust it to your own URL each time.
In this section we're going to prepare the system with some basic settings:
• Make sure the system is updated with the following commands:
$ sudo apt update && sudo apt upgrade
• Update the hosts file (/etc/hosts) with the hostname and the Team Password Manager URL. To do it:
1. Get the hostname of your computer with this command: $ hostname
2. Edit /etc/hosts and enter the following line:
IP ADDRESS hostname tpm.mycompany.com
If, for instance, the IP address ofyour server is 1.2.3.4 and your hostname is tpm-hostname, this line should be:
1.2.3.4 tpm-hostname tpm.mycompany.com
• Set the timezone of your server. Here we set it to UTC with the following command:
$ sudo timedatectl set-timezone UTC
See all the timezones you can use with: timedatectl list-timezones
Check with date:
Sun Mar 9 05:49:46 UTC 2025
• Enable the firewall (ufw), also enabling SSH through it. Execute these two commands to do it:
$ sudo ufw allow ssh
$ sudo ufw enable
• Turn on network time protocol (ntp) so that the server time is synced over the Internet. This is a must if you plan to use 2 factor authentication in Team Password Manager. Execute the following commands to enable ntp:
$ sudo timedatectl set-ntp on
$ sudo ufw allow ntp
Apache 2.4 installation
We'll be using Apache 2.4 as our web server. To install it use the following commands:
$ sudo add-apt-repository ppa:ondrej/apache2
$ sudo apt update
$ sudo apt install apache2
Once it's installed let's configure a couple of things:
• Enable http and https ports (80, 443) through the firewall:
$ sudo ufw allow in "Apache Full"
• Disable Apache MPM event and enable Apache MPM prefork. Execute the following commands:
$ sudo a2dismod mpm_event
$ sudo a2enmod mpm_prefork
And finally restart Apache with this command:
$ sudo systemctl restart apache2
To test that Apache is running in your server you can open a web browser and type the IP address of your server in the address bar. If everything is ok you should see the following Apache default page:
MySQL 8 installation
We're going to use MySQL 8 as the database for Team Password Manager. MySQL 8 is the default version of MySQL that installs with Ubuntu 24.04, so to install just use this command:
$ sudo apt install mysql-server
Once it's installed, run the security script to set the root password and some additional settings:
$ sudo mysql_secure_installation
You can safely set the following options in the script:
- Medium level of the password validation policy (Length >= 8, numeric, mixed case, and special characters).
- Remove anonymous users.
- Disallow root login remotely.
- Remove test database and access to it.
Once the script is finished you can test the connection using the following command:
$ sudo mysql
This will connect to the MySQL console using root because you're using sudo.
You'll be placed at the MySQL prompt: mysql>. Just type exit to return to the system prompt.
PHP 8.4 installation
Since PHP 8.4 is not the default version of PHP in Ubuntu 24.04, we'll need to add the Ondřej Surý PPA into our system. To do it, execute these two commands:
$ sudo add-apt-repository ppa:ondrej/php
$ sudo apt update
After that, to install PHP and the modules that are required to run Team Password Manager, enter this command:
$ sudo apt install php8.4 libapache2-mod-php8.4 php8.4-common php8.4-cli php8.4-mysql php8.4-mbstring php8.4-ldap php8.4-curl php8.4-gd php8.4-xml
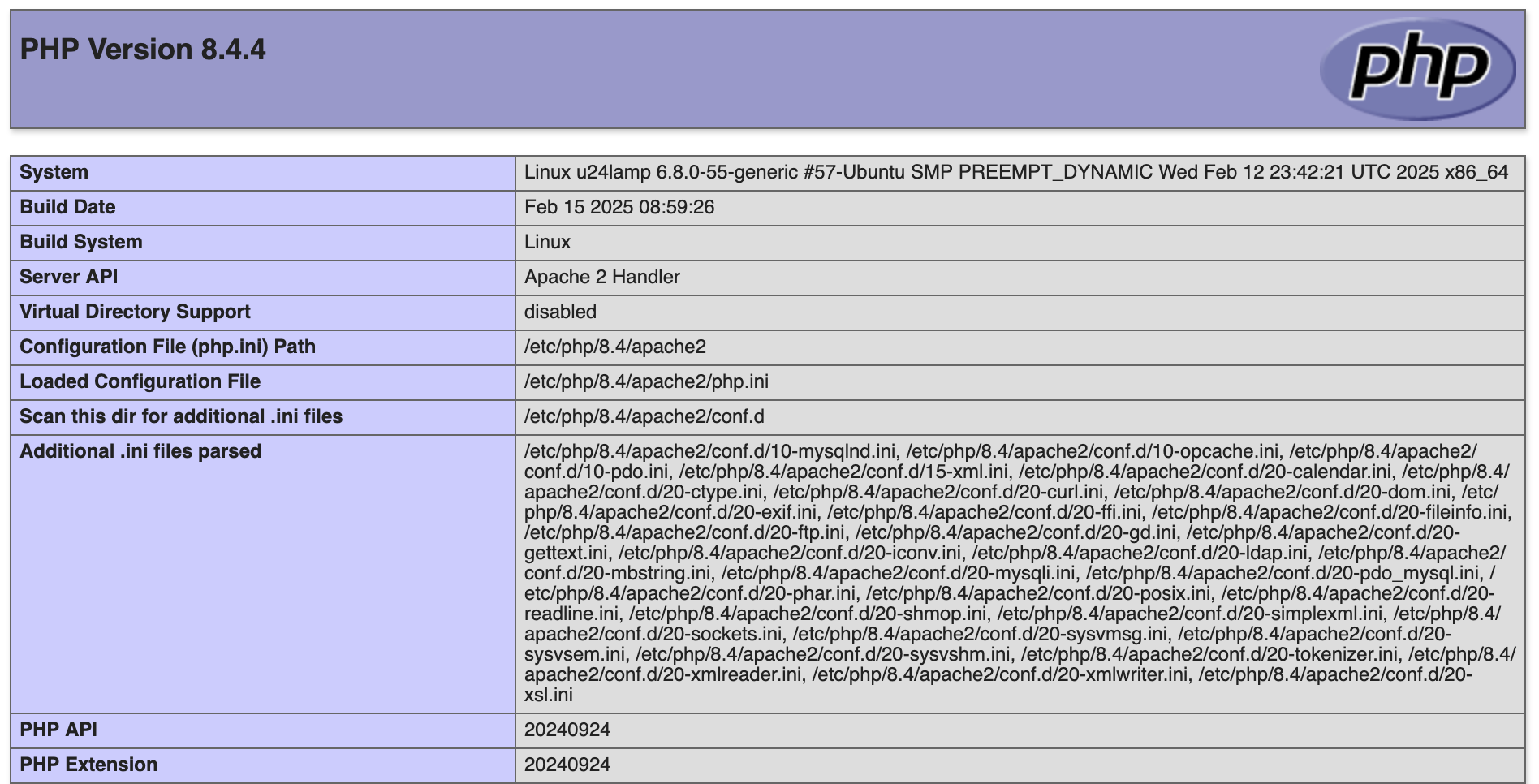
Check that you've installed the correct PHP version using this command: $ php -v. You should see an output similar to this one:
PHP 8.4.4 (cli) (built: Feb 15 2025 08:59:26) (NTS)
Copyright (c) The PHP Group
Zend Engine v4.4.4, Copyright (c) Zend Technologies
with Zend OPcache v8.4.4, Copyright (c), by Zend Technologies
Set PHP's timezone to match the one of your server's: edit /etc/php/8.4/apache2/php.ini and set the following entry with the same timezone you set in the Basic settings section (all the PHP timezones can be found here: https://www.php.net/manual/en/timezones.php). In our case we set it to "UTC":
date.timezone = "UTC"
After this, restart Apache:
$ sudo systemctl restart apache2
To check that PHP is correctly installed and communicating with Apache, do this:
1. Create a file called phpinfo.php in /var/www/html/ with the following content:
<?php phpinfo();
2. Open this file with the browser pointing at your IP address: http://IP_ADDRESS/phpinfo.php
You should see the phpinfo page with all the PHP settings. You can send this to PDF to keep it for your records. Afterwards, delete the phpinfo.php file.
Configuring the web server to run our Team Password Manager installation using Virtual hosts
As stated earlier, we're going to access the Team Password Manager installation using this URL: https://tpm.mycompany.com. To make this possible, you need to do two things:
1. Create a new A/AAAA record in your DNS manager so that tpm.mycompany.com resolves to the server's IP address.
2. Configure a virtual host in Apache to accept tpm.mycompany.com (for port 80 (http) and 443 (https)) and make it execute the Team Password Manager installation.
Let's explain them in more detail:
1. Go to the DNS manager for your domain and create an A record (AAAA if IPv6) for your tpm.mycompany.com subdomain, specifying the IP address of your server and the default TTL value if you need to set one. To test open the browser and enter tpm.mycompany.com in the address bar. You should see the Apache default page. Note that this can take a while to propagate through all the DNS servers so it's normal if you don't see this immediately. Just wait for a few minutes.
2. Virtual hosts: virtual hosts allow your Apache server to serve more than one site and configure each site with their own set of options. In this case, "site" is the Team Password Manager installation. We'll configure one virtual host to serve tpm.mycompany.com. First we'll do the configuration for http://tpm.mycompany.com and later we'll configure https://tpm.mycompany.com with a commercial SSL certificate. Please follow these steps (remember always to change tpm.mycompany.com to your own subdomain):
2.1 Create a copy of the default Apache configuration file for the Team Password Manager site:
$ sudo cp /etc/apache2/sites-available/000-default.conf /etc/apache2/sites-available/tpm.mycompany.com.conf
2.2 Edit the tpm.mycompany.com.conf configuration file to look like this:
<Directory /var/www/html/tpm.mycompany.com/public_html> Require all granted AllowOverride All Options FollowSymLinks </Directory> <VirtualHost *:80> ServerName tpm.mycompany.com ServerAlias tpm.mycompany.com ServerAdmin info@mycompany.com DocumentRoot /var/www/html/tpm.mycompany.com/public_html ErrorLog /var/www/html/tpm.mycompany.com/logs/error.log CustomLog /var/www/html/tpm.mycompany.com/logs/access.log combined </VirtualHost>
Some explanations:
/var/www/html/tpm.mycompany.com/public_htmlis where we'll put the Team Password Manager software files. We'll do this later on this tutorial. TheDocumentRootdirective is used to tell the web server that when a request is made to tpm.mycompany.com it should serve the files on /var/www/html/tpm.mycompany.com/public_html.- The
ErrorLogandCustomLogdirectives create specific logs for our installation, which are stored in/var/www/html/tpm.mycompany.com/logs/. Note that these logs are web server logs, not the internal log of Team Password Manager (which can be found in the top menu of the software, "Log" option). - We've also set the following options in the site folder:
Require all granted: all IP addresses can access the site,AllowOverride All: allows .htaccess files in folders to override the Apache configuration andOptions FollowSymLinksdisables directory listing for security.
2.3 Create the installation folders:
Execute this command to create the folders for Team Password Manager and logs:
$ sudo mkdir -p /var/www/html/tpm.mycompany.com/{public_html,logs}
public_html is the folder where we'll place the Team Password Manager files. logs is where the Apache logs will be written for our installation.
Both folders are currently owned by root, but it's better if you assign ownership to the Apache user and group, which for Ubuntu is www-data:
$ sudo chown -R www-data:www-data /var/www/html/tpm.mycompany.com
Then set appropriate permissions for public_html (read, write, execute for the Apache user and group, none for others):
$ sudo chmod -R 770 /var/www/html/tpm.mycompany.com/public_html
And the permissions for log (read, write, execute for the Apache user, read and execute for the Apache group, none others):
$ sudo chmod -R 750 /var/www/html/tpm.mycompany.com/logs
If you want your user to be able to create/edit files in public_html, you can add your user to www-data:
$ sudo usermod -aG www-data $USER
(you'll need to log out and log back in for this new group membership to apply)
Finally, ensure that new files and directories created within public_html and logs inherit the correct ownership and permissions by setting the setgid bit:
$ sudo chmod -R g+s /var/www/html/tpm.mycompany.com/public_html
$ sudo chmod -R g+s /var/www/html/tpm.mycompany.com/logs
The final result should be similar to this:
myuser@myhostname:/var/www/html/tpm.mycompany.com$ ls -la total 16 drwxr-xr-x 4 www-data www-data 4096 Mar 11 12:42 . drwxr-xr-x 3 root root 4096 Mar 11 12:42 .. drwxr-s--- 2 www-data www-data 4096 Mar 11 12:49 logs drwxrws--- 7 www-data www-data 4096 Mar 11 19:29 public_html
2.4 Enable the site:
$ sudo a2ensite tpm.mycompany.com
Disable the default virtual host to minimize security risks:
$ sudo a2dissite 000-default.conf
And finally reload Apache:
$ sudo systemctl reload apache2
To test, enter http://tpm.mycompany.com/ in your browser and you should see this forbidden message as we haven't yet put any files in the public_html folder (and also due to Options FollowSymLinks):
Also, after accessing it, check the logs folder and you'll see the two log files: access.log and error.log.
HTTPS and installing an SSL Certificate from a Commercial Certificate Authority
Up to this point we've configured the server to accept requests to http://tpm.mycompany.com.
In this section we'll:
- Install a commercial SSL certificate to avoid browser warnings about unsafe connections.
- Configure the web server to accept requests to https://tpm.mycompany.com (note the "s" in https), so that the communication between the client's browser and the server is encrypted.
Let's get to it. We'll first begin by changing to root user and updating the system:
$ su - root (and enter the root password)
# apt update && apt upgrade
To get a commercial SSL certificate we'll need a private key and a Certificate Signing Request (CSR) file. You can create them using the following commands:
Create a folder where to store the certificate files and go to that folder:
# mkdir /root/certs/ && cd /root/certs/
Execute openssl to create the private key and CSR (remember to use your own subdomain instead of tpm.mycompany.com):
# openssl req -new -newkey rsa:2048 -nodes -keyout tpm.mycompany.com.key -out tpm.mycompany.com.csr
When you execute this you'll be required to enter some information that will be integrated into your certificate request. It's specially important that you correctly enter the "Common name", which is the URL you want to use to access your installation of Team Password Manager. In this case we've used tpm.mycompany.com because we'll use https://tpm.mycompany.com to access our Team Password Manager installation (marked in red):
Generating a RSA private key
.....................+++++
......+++++
writing new private key to 'tpm.mycompany.com.key'
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:ES
State or Province Name (full name) [Some-State]:Barcelona
Locality Name (eg, city) []:My city
Organization Name (eg, company) [Internet Widgits Pty Ltd]:My company
Organizational Unit Name (eg, section) []:Security
Common Name (e.g. server FQDN or YOUR name) []:tpm.mycompany.com
Email Address []:info@mycompany.com
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
The outcome of executing openssl are two files: tpm.mycompany.com.key and tpm.mycompany.com.csr.
tpm.mycompany.com.key is the private key, and you should protect it and not disclose it to anyone. tpm.mycompany.com.csr is the CSR file. You'll be required to copy and paste its contents into the online enrollment form when requesting the certificate.
You should now purchase the certificate from a Commercial Authority (CA). We've used Namecheap (PositiveSSL certificate) but you can use any CA that you like. The CA will ask you to copy the information in the CSR file (everything from -----BEGIN CERTIFICATE REQUEST to END CERTIFICATE REQUEST-----) and paste it on the indicated form. You can see the contents of the CSR file with this command: # cat tpm.mycompany.com.csr. You'll also need to validate your domain, the CA will provide various methods for doing so.
The CA will provide you with two files: tpm_mycompany_com.crt and tpm_mycompany_com.ca-bundle. Once you have them continue with the following steps:
Copy the files to the appropriate folders:
# cp tpm_mycompany_com.crt /etc/ssl/certs/ # cp tpm_mycompany_com.ca-bundle /etc/ssl/certs/ # cp tpm.mycompany.com.key /etc/ssl/private/ # cp tpm.mycompany.com.csr /etc/ssl/private/
Delete them from the /root/cert folder:
# rm /root/cert/tpm*
Note: we advise you to store all the certificate files outside the server, in a backup location.
The certificate files should be owned by root and protected by a permission setting of 600:
# chown root: /etc/ssl/private/tpm* # chown root: /etc/ssl/certs/tpm* # chmod 0600 /etc/ssl/private/tpm* # chmod 0600 /etc/ssl/certs/tpm*
So the result of installing the certificate files should be something like this:
# ls -la /etc/ssl/certs/tpm* -rw------- 1 root root 4135 Mar 10 15:24 /etc/ssl/certs/tpm_mycompany_com.ca-bundle -rw------- 1 root root 2216 Mar 10 15:24 /etc/ssl/certs/tpm_mycompany_com.crt # ls -la /etc/ssl/private/tpm* -rw------- 1 root root 1102 Mar 10 15:24 /etc/ssl/private/tpm.mycompany.com.csr -rw------- 1 root root 1704 Mar 10 15:24 /etc/ssl/private/tpm.mycompany.com.key
Let's now tackle the Apache configuration part.
Activate the ssl and headers modules:
# a2enmod ssl
# a2enmod headers
Restart Apache:
# systemctl restart apache2
We'll now edit the virtual host configuration file we created in the previous section (/etc/apache2/sites-available/tpm.mycompany.com.conf) to a) redirect http to https and 2) configure https. So edit this file to make it look like this, as always replacing tpm.mycompany.com with your own subdomain (we've marked the new lines in blue):
<Directory /var/www/html/tpm.mycompany.com/public_html> Require all granted AllowOverride All Options FollowSymLinks </Directory> <VirtualHost *:80> ServerName tpm.mycompany.com ServerAlias tpm.mycompany.com ServerAdmin info@mycompany.com DocumentRoot /var/www/html/tpm.mycompany.com/public_html ErrorLog /var/www/html/tpm.mycompany.com/logs/error.log CustomLog /var/www/html/tpm.mycompany.com/logs/access.log combined Redirect 301 / https://tpm.mycompany.com/ </VirtualHost> <VirtualHost *:443> ServerAdmin info@mycompany.com ServerName tpm.mycompany.com ServerAlias tpm.mycompany.com DocumentRoot /var/www/html/tpm.mycompany.com/public_html ErrorLog /var/www/html/tpm.mycompany.com/logs/error.log CustomLog /var/www/html/tpm.mycompany.com/logs/access.log combined SSLEngine on SSLCertificateFile /etc/ssl/certs/tpm_mycompany_com.crt SSLCertificateKeyFile /etc/ssl/private/tpm.mycompany.com.key SSLCertificateChainFile /etc/ssl/certs/tpm_mycompany_com.ca-bundle # HSTS (mod_headers is required) (15768000 seconds = 6 months) Header always set Strict-Transport-Security "max-age=15768000" </VirtualHost>
Let me explain some of the changes we've introduced:
- The
<VirtualHost *:80>section now has a new directive,Redirect, which we use to redirect the non encrypted requests (http) to the encrypted ones (https). So, even if a user goes to http://tpm.mycompany.com, she'll be automatically redirected to https://tpm.mycompany.com. - We've created a new section (
<VirtualHost *:443>) to configure https, to respond to requests made to https://tpm.mycompany.com. The information is the same of the non-ssl section but with the SSL directives.
Finally, reload Apache for the changes to take effect:
# systemctl reload apache2
You should also exit to get out of root return to the normal user.
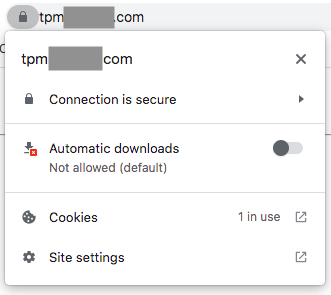
You can now test the requests: if you go to http://tpm.mycompany.com, you should be redirected to https://tpm.mycompany.com, and see the same forbidden message as before (as we still haven't installed the software files). This time, though, you can see that the browser shows you the secure connection "lock" icon and if you click on it you'll find information about the certificate:
SourceGuardian Loader installation
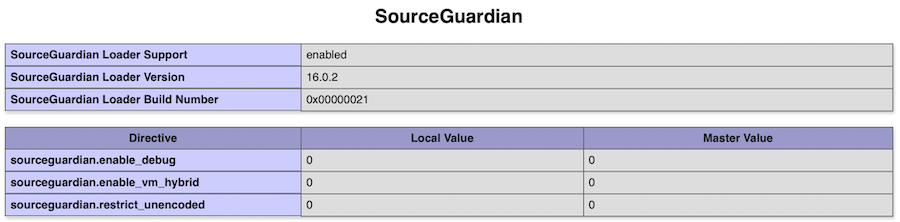
Team Password Manager is a PHP web application encoded and secured using an encoder (SourceGuardian) and a loader is required to execute it. You need at least version 16.0.0 of the SourceGuardian Loader.
To install the Sourceguardian Loader follow these steps:
Go to https://www.sourceguardian.com/loaders.html and download the Linux x86_64 zip package. You should get the following file: loaders.linux-x86_64.zip.
Unzip it (it will create the "loaders.linux-x86_64" folder) and copy (or upload) the ixed.8.4.lin file into the following folder on your server: /usr/lib/php/20240924.
Edit the php.ini file in /etc/php/8.4/apache2/php.ini and put this line just below [PHP]:
extension=ixed.8.4.lin
Restart Apache:
$ sudo systemctl restart apache2
To test: create a file called phpinfo.php in /var/www/html/tpm.mycompany.com/public_html with this content:
<?php phpinfo();
Open this file with the browser: https://tpm.mycompany.com/phpinfo.php
Check the "Sourceguardian" section, like in this image (note that for this tutorial the Loader version should be 16+):
Delete the phpinfo.php file.
Team Password Manager database and user
In this section we're going to create the database that will store the Team Password Manager information and a user to access this database from the software. We're going to use these values, we advise you use your own:
Database: tpm_database
User: tpm_user
Password: tpmPass%2025
Follow these steps to create the database and user:
1. Enter the mysql prompt. Since we're using sudo, we'll log in with the mysql root user:
$ sudo mysql
2. Type the following command at the mysql prompt to create the database:
mysql> CREATE DATABASE `tpm_database` CHARACTER SET utf8 COLLATE utf8_unicode_ci;
3. Type the following command at the mysql prompt to create the user:
mysql> CREATE USER 'tpm_user'@'%' IDENTIFIED BY 'tpmPass%2025';
3. Type the following commands at the mysql prompt to grant all the privileges to the user on the database:
mysql> GRANT ALL ON tpm_database.* TO 'tpm_user'@'%';
mysql> FLUSH PRIVILEGES;
Type exit at the mysql prompt to exit mysql and return to the normal linux prompt.
Team Password Manager files
Download the Team Password Manager software files from https://teampasswordmanager.com/download/, unzip the zip file and upload all the files and folders to /var/www/html/tpm.mycompany.com/public_html.
Let's now verify permissions. We're going to assign the following permissions to Team Password Manager files and folders: full to the user and group and none to the others (770):
$ chmod -R 770 *
You should have something like this when done (myuser is the user you're using to create the installation; also note that at the time of writing this tutorial the version of Team Password Manager used is 14.168.293, so you might have different file sizes):
$ ls -la drwxrws--- 7 www-data www-data 4096 Mar 10 15:59 . drwxr-xr-x 4 www-data www-data 4096 Mar 10 12:08 .. -rwxrwx--- 1 myuser www-data 1873 Mar 10 15:59 config.php drwxrws--- 3 myuser www-data 4096 Mar 10 15:59 css -rwxrwx--- 1 myuser www-data 9262 Mar 10 15:59 eula.txt -rwxrwx--- 1 myuser www-data 610 Mar 10 15:59 folder.php drwxrws--- 2 myuser www-data 4096 Mar 10 15:59 import -rwxrwx--- 1 myuser www-data 32640 Mar 10 15:59 index.php -rwxrwx--- 1 myuser www-data 10157 Mar 10 15:59 install.txt -rwxrwx--- 1 myuser www-data 25 Mar 10 15:59 robots.txt drwxrws--- 8 myuser www-data 4096 Mar 10 15:59 system -rwxrwx--- 1 myuser www-data 4651 Mar 10 15:59 upgrade.txt drwxrws--- 2 myuser www-data 4096 Mar 10 15:59 uploads drwxrws--- 17 myuser www-data 4096 Mar 10 15:59 wmm
Team Password Manager configuration file (config.php)
Edit the config.php file and enter the database, user and password configured in the database step:
// MySQL Database server
define('CONFIG_HOSTNAME', 'localhost');
// User that accesses the database server, that should have all privileges on the database CONFIG_DATABASE
define('CONFIG_USERNAME', 'tpm_user');
// User password
define('CONFIG_PASSWORD', 'tpmPass%2025');
// Database for Team Password Manager. You must manually create it before installing Team Password Manager
define('CONFIG_DATABASE', 'tpm_database');
Team Password Manager installation script
Open your browser and enter this in the address bar:
https://tpm.mycompany.com/index.php/install
You should see the Team Password Manager installation screen:
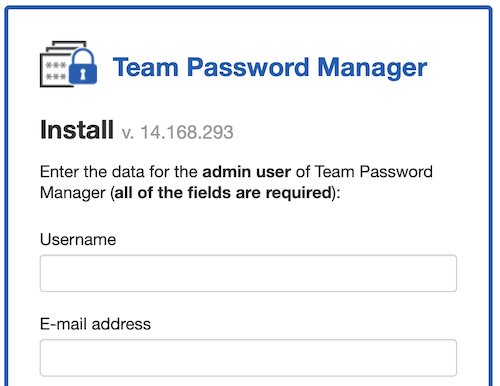
Just enter the values and complete the installation.
If everything went well Team Password Manager is now installed. Congratulations!!
Document changelog
| Mar 12, 2025: | Document created, replacing the Ubuntu 22.04 one |
